DSchap08
-
Upload
muhammad-hashim -
Category
Documents
-
view
215 -
download
0
Transcript of DSchap08
-
8/3/2019 DSchap08
1/33
Search Algorithms
1
Chapter 8
11
-
8/3/2019 DSchap08
2/33
Chapter Objectives
Data Structures Using Java2
y Learn the various search algorithms
y Explore how to implement the sequential and binarysearch algorithms
y
Discover how the sequential and binary searchalgorithms perform
y Learn about hashing
-
8/3/2019 DSchap08
3/33
class ArrayListClass: Basic Operations
Data Structures Using Java3
y isEmpty
y isFull
y listSize
y maxListSixey Print
y isItemAtEqual
y insertAt
y insertEnd
y removeAt
y retrieveAt
y replaceAt
y clearListy seqSearch
y insert
y remove
y copyList
-
8/3/2019 DSchap08
4/33
Search Algorithms
Data Structures Using Java4
y Associated with each item in a data set is a specialmember (the key of the item) that uniquely identifies theitem in the data set
y
Keys are used in such operations as searching, sorting,insertion, and deletion
y Analysis of the algorithms enables programmers todecide which algorithm to use for a specific application
-
8/3/2019 DSchap08
5/33
Sequential Search
Data Structures Using Java5
y Starts at the first element in the list
y Continues until either the item is found in the list or the
entire list is searched
y Works the same for both array-based and linked lists
-
8/3/2019 DSchap08
6/33
Sequential Search
Data Structures Using Java6
public int seqSearch(DataElement searchItem){
int loc;boolean found = false;for(loc = 0; loc < length; loc++)
if(list[loc].equals(searchItem)){found = true;
break;}
if(found)
return loc;else
return -1;}//end seqSearch
-
8/3/2019 DSchap08
7/33
Search Algorithms
Data Structures Using Java7
y Search item: target
y To determine the average number of comparisons in the
successful case of the sequential search algorithm:
y Consider all possible casesy Find the number of comparisons for each case
y Add the number of comparisons and divide by the number of
cases
-
8/3/2019 DSchap08
8/33
Sequential Search Analysis
Data Structures Using Java8
Suppose that there are n elements in the list. The following
expression gives the average number of comparisons:
It is known that
Therefore, the following expression gives the average number ofcomparisons made by the sequential search in the successful case:
-
8/3/2019 DSchap08
9/33
Ordered Lists as Arrays
Data Structures Using Java9
y List is ordered if its elements are ordered according to somecriteria
y Elements of a list usually in ascending order
y Define ordered list as an ADT
-
8/3/2019 DSchap08
10/33
Ordered Lists as Arrays
Data Structures Using Java10
y Several operations can be performed on an ordered list;similar to the operations performed on an arbitrary listy Determining whether the list is empty or fully Determining the length of the listy Printing the listy Clearing the list
y Using inheritance, derive class to implement ordered lists
from class ArrayListClass
-
8/3/2019 DSchap08
11/33
Binary Search Algorithm
Data Structures Using Java11
y Very fast
y Uses divide and conquer technique to search list
y First, search item compared with middle element of list
y If the search item is less than middle element of list,restrict the search to first half of list
y Otherwise, search second half of list
-
8/3/2019 DSchap08
12/33
-
8/3/2019 DSchap08
13/33
Binary Search: middle element
Data Structures Using Java13
first + last
2mid =
-
8/3/2019 DSchap08
14/33
Binary Search
Data Structures Using Java14
public int binarySearch(DataElement item){
int first = 0;int last = length - 1;int mid = -1;
boolean found = false;while(first 0)
last = mid - 1;else
first = mid + 1;
}if(found)
return mid;else
return -1;}//end binarySearch
-
8/3/2019 DSchap08
15/33
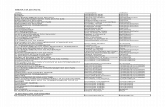
Binary Search: Example
Data Structures Using Java15
-
8/3/2019 DSchap08
16/33
Binary Search: Example
Data Structures Using Java16
Unsuccessful search
Total number of comparisons is 6
-
8/3/2019 DSchap08
17/33
Performance of Binary Search
Data Structures Using Java17
y Unsuccessful search
y for a list of length n, a binary search makes approximately
2*log2(n + 1) key comparisons
y Successful search
y for a list of length n, on average, a binary search makes 2*log2n
4 key comparisons
-
8/3/2019 DSchap08
18/33
Algorithm to Insert into an Ordered List
Data Structures Using Java18
Use algorithm similar to binary search algorithm to findplace where item is to be inserted
if the item is already in this listoutput an appropriate message
elseuse the method insertAt to insert the item in
the list
-
8/3/2019 DSchap08
19/33
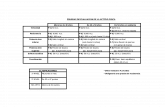
Search Algorithm Analysis Summary
Data Structures Using Java19
-
8/3/2019 DSchap08
20/33
Hashing
Data Structures Using Java20
y Main objectives to choosing hash methods:
y Choose a hash method that is easy to compute
y Minimize the number of collisions
-
8/3/2019 DSchap08
21/33
Commonly Used Hash Methods
Data Structures Using Java21
y Mid-Square
y Hash method, h, computed by squaring the identifier
y Using appropriate number of bits from the middle of the square
to obtain the bucket address
y Middle bits of a square usually depend on all the characters, it is
expected that different keys will yield different hash addresses
with high probability, even if some of the characters are the
same
-
8/3/2019 DSchap08
22/33
Commonly Used Hash Methods
Data Structures Using Java22
y Folding
y Key Xis partitioned into parts such that all the parts, except
possibly the last parts, are of equal length
y Parts then added, in convenient way, to obtain hash address
y Division (Modular arithmetic)
y Key Xis converted into an integer iX
y This integer divided by size of hash table to get remainder,
giving address ofXin HT
-
8/3/2019 DSchap08
23/33
Commonly Used Hash Methods
Data Structures Using Java23
Suppose that each key is a string. The following Java
method uses the division method to compute the address
of the key:
int hashmethod(String insertKey)
{
int sum = 0;
for(int j = 0; j
-
8/3/2019 DSchap08
24/33
Collision Resolution
Data Structures Using Java24
y Algorithms to handle collisions
y Two categories of collision resolution techniques
y Open addressing (closed hashing)
y
Chaining (open hashing)
-
8/3/2019 DSchap08
25/33
Open Addressing: Linear Probing
Data Structures Using Java25
y Suppose that an item with key Xis to be inserted in HT
y Use hash function to compute index h(X) of item in HT
y Suppose h(X) = t. Then 0 = h(X) = HTSize 1
y IfHT[t] is empty, store item into array slot.y Suppose HT[t] already occupied by another item;
collision occurs
y Linear probing: starting at location t, search array
sequentially to find next available array slot
-
8/3/2019 DSchap08
26/33
Collision Resolution:
Open Addressing
Data Structures Using Java26
Pseudocode implementing linear probing:
hIndex = hashmethod(insertKey);
found = false;
while(HT[hIndex] != emptyKey && !found)
if(HT[hIndex].key == key)
found = true;
else
hIndex = (hIndex + 1) % HTSize;
if(found)
System.out.println(Duplicate items not allowed);
else
HT[hIndex] = newItem;
-
8/3/2019 DSchap08
27/33
Linear Probing
Data Structures Using Java27
-
8/3/2019 DSchap08
28/33
Random Probing
Data Structures Using Java28
y Uses a random number generator to find the nextavailable slot
y ith slot in the probe sequence is: (h(X) + ri) % HTSizewhere ri is the ith value in a random permutation of thenumbers 1 to HTSize 1
y All insertions and searches use the same sequence ofrandom numbers
-
8/3/2019 DSchap08
29/33
Quadratic Probing
Data Structures Using Java29
y Reduces primary clustering
y We do not know if it probes all the positions in the table
y When HTSize is prime, quadratic probing probes about
half the table before repeating the probe sequence
-
8/3/2019 DSchap08
30/33
Deletion: Open Addressing
Data Structures Using Java30
y In open addressing, when an item is deleted, its position
in the array cannot be marked as empty
-
8/3/2019 DSchap08
31/33
Deletion: Open Addressing
Data Structures Using Java31
-
8/3/2019 DSchap08
32/33
Deletion: Open Addressing
Data Structures Using Java32
-
8/3/2019 DSchap08
33/33
Chapter Summary
Data Structures Using Java33
y Search Algorithms
y Sequential
y Binary
y Algorithm Analysis
y Hashing
y Hash Table
y Hash method
y Collision Resolution