tshark.pdf
-
Upload
elputoamo-xd -
Category
Documents
-
view
216 -
download
0
Transcript of tshark.pdf
-
8/15/2019 tshark.pdf
1/5
Tshark: Strip WPA Wireless Captures by ESSID with Tshark
purehate March 29, 2010 Insights 13 Comments
Code Snippets
Errors
Insights
Labs
Security
Backtrack Linux
Consulting
Contact
Documentation
Kali Linux
Tags
Tools
Home » Insights »
Tshark: Strip WPA Wireless Captures by ESSID with Tshark
Tweet
2A while ago I wrote a short tutorial on how to strip down a wireless capture which contained a wpa handshake
so that only eapol packets and beacon frames where left. I have since found a little bit better way to do it so I
decided to make a new post. In the previous article I showed how to strip by wlan.mgt frames containing the
mac address. The problem with this is that it strips out lots of other packets which some programs use to
check for ESSID. I looked into the issue some more and found a way to strip just by essid.
If you just want the command:
Obviously you have to have tshark installed for this to work.
I also had a customer for our online wpa cracker server who was having trouble stripping a capture so I decided to whip
up a quick shell script to help him out.
If you want to use this simply create a �le called stripper.sh and paste this script into it.
Next make the script executable by issuing the command:
Once you have done that simply run the script.
Example of script being run:
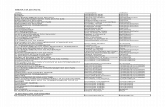
tshark -r -R "eapol || wlan_mgt.tag.interpretation eq || (wlan.fc.type_s"eapol || wlan_mgt.tag.interpretation eq || (wlan.fc.type_s
#!/bin/bash#!/bin/bash
echoecho "This script requires tshark""This script requires tshark"
echoecho
echoecho "Checking for tshark""Checking for tshark"
typetype tshark &>tshark &>/dev/null/dev/null || {|| { echoecho "I require tshark but it's not installed. Aborting.""I require tshark but it's not installed. Aborting." >&2;>&2;
echoecho "tshark found""tshark found"
echoecho
echoecho "Moving on....""Moving on...."
echoecho
echoecho "Please the path to the capture (ex. /home/john/NETGEAR.cap)""Please the path to the capture (ex. /home/john/NETGEAR.cap)"
readread cap_pathcap_path
echoecho
whilewhile [ ! -f[ ! -f "$cap_path""$cap_path" ];];dodo
echoecho
echoecho "File cannot be found or does not exist""File cannot be found or does not exist"
echoecho
echoecho "Please the path to the capture (ex. /home/john/NETGEAR.cap):""Please the path to the capture (ex. /home/john/NETGEAR.cap):"
readread cap_pathcap_path
donedone
echoecho
echoecho "Please enter the ESSID (ex. NETGEAR)""Please enter the ESSID (ex. NETGEAR)"
readread essidessid
whilewhile [ -z[ -z "$essid""$essid" ];]; dodo
echoecho "You still didnt enter any data n00b""You still didnt enter any data n00b"
echoecho
echoecho "Please enter the ESSID (ex. NETGEAR)""Please enter the ESSID (ex. NETGEAR)"
readread essidessid
donedone
echoecho
echoecho "Stripping file....""Stripping file...."
tshark -r $cap_path -Rtshark -r $cap_path -R "eapol || wlan_mgt.tag.interpretation eq $essid || (wlan.fc.type_subty"eapol || wlan_mgt.tag.interpretation eq $essid || (wlan.fc.type_subty
echoecho
echoecho "Your stripped file should be located in the current directory and named stripped.cap.""Your stripped file should be located in the current directory and named stripped.cap."
chmodchmod 755 stripper.sh755 stripper.sh
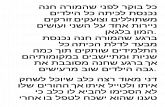
[root@dev-tools ~][root@dev-tools ~]# ./strip.sh# ./strip.sh
This script requires tsharkThis script requires tshark
CheckingChecking forfor tsharktshark
tshark foundtshark found
Moving on....Moving on....
Search here..
How to Con�gure NVFax on
FreePBX
TextMate Find & Replace Using
Regular Expressions
CentOS Remove Old Kernels
CATEGORIES
PAGES
LATEST ARTICLES
Tshark: Strip WPA Wireless Captures by ESSID wi... http://www.question-defense.com/2010/03/29/tsh
de 5 06/01/15 21
-
8/15/2019 tshark.pdf
2/5
SHARE
Previous
make: yacc: Command not foundon Cent OS
Next
no such �le to load — rubygems(LoadError)
WLAN_7E6E 8:48 PM July 11, 2011
CRACIAS
Reply
ALEX 11:05 AM Apr il 4 , 2012
Hello WLAN_7E6E,
No problem. Thanks for taking the time to leave feedback.
Thanks.
alex
Reply
PETRU 7:27 AM November 3 , 2011
Yup, verrrry interesting and educational .You guys are still the best ( I mean
americans , cose I´m
not an american) .
I think I´l use y our WPA cracker too . Till the next time, bee healty and have fun .
Reply
ALEX 11:09 AM Apr il 4 , 2012
Please the path to the capture (ex.Please the path to the capture (ex. /home/john/NETGEAR/home/john/NETGEAR.cap).cap)
/root/old/root/old.cap.cap
Please enter the ESSID (ex. NETGEAR)Please enter the ESSID (ex. NETGEAR)
NEUF_A268NEUF_A268
StrippingStripping filefile........
Running as userRunning as user "root""root" and groupand group "root""root". This could be dangerous.. This could be dangerous.
Your strippedYour stripped filefile should be locatedshould be located inin the current directory and named stripped.cap.the current directory and named stripped.cap.
TOPICS BEACON CAPTURE DATA EAPOL FRAME STRIPPED TSHARK WPA
How To Tell Exactly How Many
Spaces A ESSID Includes Using
airodump-ng Or Wireshark
Strip WPA Capture File Down To
EAPOL Packets Based On BSSID
Instead Of ESSID
View Wireless Authentication
Type Using Wireshark In Network
Capture: PSK, WPA
Related Posts
There are 13 Comments.
Tshark: Strip WPA Wireless Captures by ESSID wi... http://www.question-defense.com/2010/03/29/tsh
2 de 5 06/01/15 21
-
8/15/2019 tshark.pdf
3/5
Hello Petru,
Thanks for the compliment. We however support a world where all are equal
and we share the same respect for all regardless of birthplace. Sorry for the
delayed response… got overwhelmed with comments and just now trying to
catch up. Anyhow hope you �nd our online password audit/password cracking
services at http://tools.question-defense.com useful and valuable.
Anyhow thanks for taking the time to post feedback on our site.
Thanks.
alex
Reply
FAISAL 3:02 AM Apr il 4 , 2012
hello sir already have password in handshake capture �le how can see that
password
Reply
ALEX 11:12 AM Apr il 4 , 2012
Hello faisal,
You would need to use either software such as oclHashcat+ or aircrack-ng or an
online service like ours located at http://tools.question-defense.com. Good luck
and thanks for leaving feedback!
Thanks.
alex
Reply
COMPILINGENTROPY 5:54 PM December 6 , 2012
Hmm, it seems your website thinks part of my command is html. here’s the
actual command (last time!):
tshark -r [input �le] -R “eapol || wlan_mgt.tag.interpretation eq [essid] ||
(wlan.fc.type_subtype==0×08 && wlan_mgt.ssid eq [essid]) && wlan.bssid == [bssid]” -w
[output �le]
Reply
ALEX 9:41 AM December 27, 2012
Hello compilingEntropy,
Thanks for posting this! To post code in the comments you can use the
sourcecode short code like the below with square brackets at each end… [ open
... and ] close.
OPEN_BRACKETsourcecode language=”BASH” l ight=”TRUECLOSE_BRACKET
code here
OPEN_BRACKET/sourcecodeCLOSEBRACKET
Or email what you want posted in the comment above and I will add it from
within the admin.
Again thanks for taking the time to make this observation.
Tshark: Strip WPA Wireless Captures by ESSID wi... http://www.question-defense.com/2010/03/29/tsh
3 de 5 06/01/15 21
-
8/15/2019 tshark.pdf
4/5
Thanks.
alex
Reply
IDIOTIC 8 :15 A M May 24 , 2 01 3
what an idiot way .. i have the �le in WINDOWS 2gb large .. how the f*** and
why the f*** i need to do t hat in linux moron .. show how you do it in
windows!!!
Reply
ALEX 12:33 PM May 24, 2013
Hello idiotic,
You can feel the brilliance in your comment… You don’t have to do anything in
Linux or Windows for that matter and most people stripping wireless packet
captures for this purpose do and are using Linux of some type. So glad you took
the time to shine on this post. Now we can only hope that you will bless us with
your presence again.
Thanks.
alex
Reply
@MIKE 4:42 PM October 19, 2013
it doesn’t work. maybe extract wpa handshake but beacon frame is missing, so
aircrack-ng will say unsupported �le format.
Reply
DANIEL 10:22 PM January 26, 2014
Neither this or your old post works i keep ending up with other aps and
clients but with the ssid’s st riped
This is the output i’m getting using your code:
I got it working i changed a few things
Note the brackets
Output:
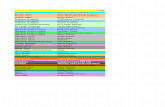
# BSSID ESSID Encryption
1 WPA (0 handshake)
2 WPA (1 handshake)
3 WPA (0 handshake)
4 WPA (0 handshake)
5 WPA (0 handshake)
6 WPA (1 handshake)
7 WPA (1 handshake)
8 WPA (0 handshake)
9 WPA (0 handshake)
10 WPA (0 handshake)11 WPA (0 handshake)
12 EAPOL+WPA (1 handshake
13 WPA (1 handshake)
14 WPA (1 handshake)
tshark -r ../dump-01.cap -R "(eapol || (wlan.fc.type_subtype == 0
Tshark: Strip WPA Wireless Captures by ESSID wi... http://www.question-defense.com/2010/03/29/tsh
4 de 5 06/01/15 21
-
8/15/2019 tshark.pdf
5/5