網路不當資訊防堵面面觀
description
Transcript of 網路不當資訊防堵面面觀

AgendaAgenda
網際網路上的不當資訊網際網路上的不當資訊
不當資訊防堵解決方案簡介不當資訊防堵解決方案簡介
Pass-ThroughPass-Through 與與 Pass-ByPass-By 防堵技術之比較防堵技術之比較
成熟的不當資訊防堵系統之必備條件成熟的不當資訊防堵系統之必備條件
相關產品比較相關產品比較
實機展示實機展示
Q & AQ & A


Source SexTracker
What percentage of
internet porn
is downloaded
from 9 to 5?

70%

IDC Research
What percentage of
workplace
Internet surfing
is not business related?

40%

WordTracker.com
What are the top 3 word searches on the
internet?MP3
Hotmail
Sex


Key Features
Comprehensive MRMAnalyzes, Reports and Manages
Internet Access
Master Database DrivenBetter categorizationNo keyword “overblocking”Automatic daily updates
Server-basedMulti-platform supportNo client-side maintenanceP
LA
TF
OR
MS
SY
ST
EM
CO
RE
AP
PL
ICA
TIO
N
MO
DU
LE
S

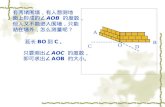
How Does it Work?
Permitted Request
Blocked Request
ActivityMonitor
Reports & Analysis
Updated Daily
User
Monitor usage Graphical reports Customizable
management
Written Policy +Rules Set-upIn Websense
WebsenseEnterprise
INTERNET
INTERNET
DATABASE
Firewall, Cache Appliance or Proxy Server

Pass-Through Technology

Pass-Through Technology(續 )

Pass-By Technology

Pass-By Technology(續 )

Pass-Through vs. Pass-By
Reliability
Scalability

成熟的不當資訊防堵系統之必備條件Over-Block vs. Under-Block
Database CoverageDatabase Accuracy
Flexible Policy ManagementPermit/BlockQuotaTime of dayPassword overrideDeferUsername/Group
Powerful ReportsCentralized Filtering Policy ManagementIntegration with Most Firewall/Proxy/Cache

相關產品比較


實機展示H/W Configuration
CPU: Pentium III 700RAM: 512 MBHD: 20 GB
S/W ConfigurationMicrosoft Windows 2000 Server SP2Microsoft ISA Server 2000 Enterprise EditionWebsense Enterprise 4.4Websense Reporter 6.3

The Top Ranked Product in EIM: Websense (www.websense.com)
The Top Ranked Product in EIM: Websense (www.websense.com)
“ When you’re ready to buy, we recommend
Websense…”— ZDNet
“Websense offers the right combination of a rich feature set and easy
administration.”— Internet Computing
“Websense is a blocking and filtering powerhouse.”
— PC Magazine
“ When you’re ready to buy, we recommend
Websense…”— ZDNet
“Websense offers the right combination of a rich feature set and easy
administration.”— Internet Computing
“Websense is a blocking and filtering powerhouse.”
— PC Magazine
SIFTSIFTFounding
Member of Secure Internet Filtering
Technology Consortia